How to Spot Suspicious or Fraudulent Emails
What safety precautions to take if you receive a fraudulent email…
In an age where phishing attempts and fraudulent emails are prevalent, it’s crucial to know how to identify these threats. Here are some quick tips to help you stay safe in your inbox:
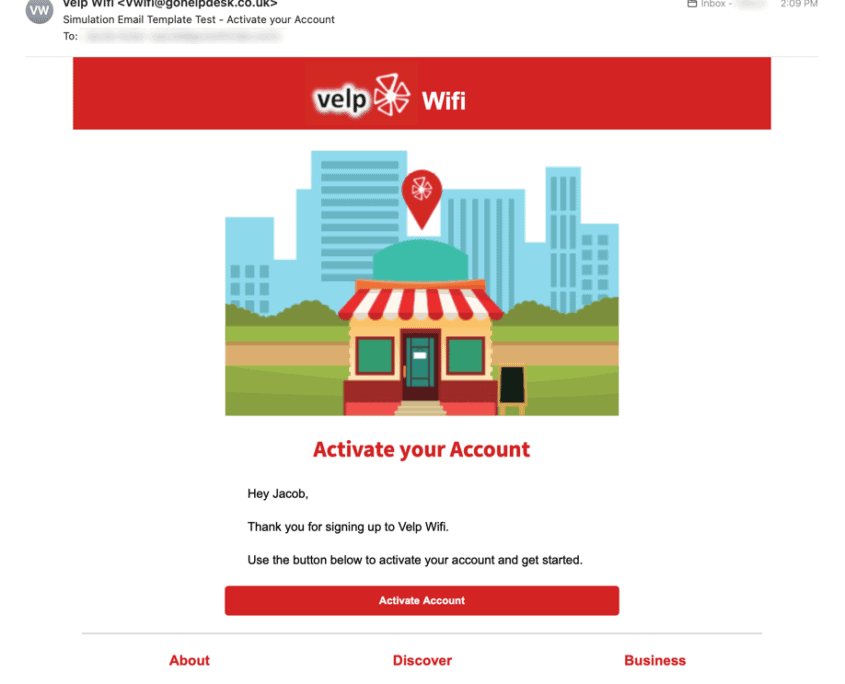
1. Check the Sender’s Email Address
Examine the sender’s email address closely. Be cautious if it seems unusual or doesn’t match the official domain of the organization they claim to represent.
2. Look for Misspelled Sender Names
Scammers often use sender names that resemble legitimate ones but contain subtle misspellings. Pay attention to these details.
3. Hover Over Links
Don’t click on links immediately. Instead, hover your mouse pointer over them to preview the destination. Ensure the URL matches the legitimate website.
4. Verify the Domain
Check the email’s domain to confirm it’s valid. Fraudulent emails may use domains that are slightly altered from the real ones.