Fast, Local IT Services in West Michigan
Expert compliant, managed IT services team to help you stay productive and secure.
We strive for excellence with a commitment to problem prevention and fast resolution when challenges arise. Beyond core managed IT services, we employ cyber security and compliance professionals to secure your data and support your regulatory compliance needs.

Trusted by your neighbors:









Trusted by your neighbors:










Effort-free comprehensive managed IT services solutions.

Step 1
Get to Know You & Collaborate
Get to Know You & Collaborate
We begin by understanding your unique IT needs and working closely with you to discuss and refine our approach. Your input is crucial to ensure our plan aligns perfectly with your goals and concerns.
Step 2
Create a Custom Plan
Create a Custom Plan
Based on our understanding, we develop a tailored strategy that addresses your specific requirements. Our recommendations are designed to fit your business precisely, avoiding one-size-fits-all solutions.
Step 3
Implement & Support
Implement & Support
After finalizing the plan, we handle the seamless implementation of new technology and continue with dedicated support. We ensure everything runs smoothly and address any issues promptly to keep your network performing optimally.


Hassle-free, efficient, and compliant managed IT services.
Enoy smooth technology with our Managed IT Services that keep things running well and reduce your stress.

Certified compliance, top-tier security.
Expert compliance and top-tier security are our specialties. We ensure your IT systems are fully protected and adhere to all best practices.



Certified compliance, top-tier security.
Expert compliance and top-tier security are our specialties. We ensure your IT systems are fully protected and adhere to all best practices.

Noteworthy IT news in West Michigan.
Organizing Your Digital Files: 11 Helpful Tips
11 of our most helpful digital file organization tips:In today's world, we rely more and more on digital files for work and personal use. That's why it's important to have a system in place for managing them. A well-organized digital filing system can save you time,...
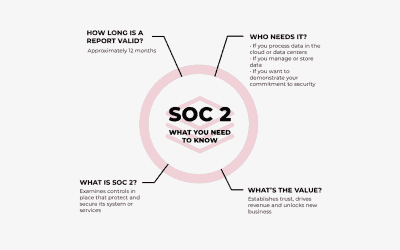
Why SOC 2 Compliance Matters for Data Security
Why is SOC 2 Compliance important?In today's digital age, the security of information has become increasingly important. Many companies rely on third-party service providers to handle sensitive information such as financial and personal data. These service providers...
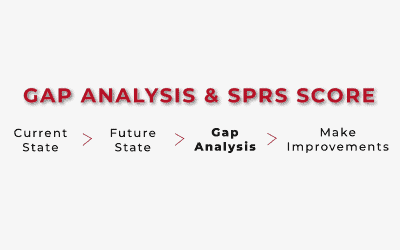
Outlining the CMMC Process: Gap Analysis and SPRS Score
Perform a Gap AnalysisWhat's a gap analysis and why is it necessary? Great question... A gap analysis is the process of identifying the gaps between your organization's current cybersecurity practices and the practices required by the CMMC framework. A gap analysis...

Everything you need to know about Managed IT Services.
What are Managed IT Services?
Managed IT Services involve outsourcing IT support, security, and infrastructure management to a specialized provider. This ensures businesses have reliable, secure, and up-to-date technology without needing an in-house IT team.
✓ Reduced downtime
✓ Enhanced security
✓ Access to IT experts
✓ Less cost than in-house IT team
How do Managed IT Services help with cybersecurity?
Managed IT providers implement 24/7 security monitoring, firewalls, endpoint protection, and regular updates to safeguard businesses from cyber threats like malware, phishing, and ransomware attacks.
✓ Continuous monitoring & threat detection
✓ Data backup & disaster recovery solutions
✓ Employee security training & phishing prevention
Do you offer 24/7 IT monitoring and support?
Yes, ICS Data provides continuous monitoring and real-time support to prevent downtime, address technical issues, and ensure systems run smoothly at all times.
✓ 24/7 helpdesk support
✓ Answer phone calls in less than 30 seconds (during business hours)
✓ Proactive system monitoring
✓ Immediate response to IT issues
How can Managed IT Services help my business scale?
Managed IT Services provide flexible, scalable solutions that grow with your business—whether you need increased cybersecurity, cloud storage, or expanded IT infrastructure.
✓ Scalable IT infrastructure & cloud solutions
✓ Flexible IT support as your company grows
✓ Custom technology strategies tailored to your goals
How can I get started with Managed IT Services for my business?
Managed IT Services provide flexible, scalable solutions that grow with your business—whether you need increased cybersecurity, cloud storage, or expanded IT infrastructure.
1. Schedule a free consultation
2. Receive a tailored IT strategy
3. Implement a seamless IT management plan